WhatsApp, being the best messaging platform to date, is not an exception to loopholes and hacks. This messenger has a vulnerability where CheckPoint researchers have exploited its XMP protocol by a self-created tool to manipulate the parameters and crash the app, repeatedly.
Group conversations are fun. And it’s one of the few reasons one sticks to the instant messaging platforms like WhatsApp. This popular messenger has a monthly active userbase of around 1.5 billion with group conversations leading the platform very actively. Aside from chit-chatting, people share important stuff and rely on this messenger for secretive communications believing it to be encrypted. What if those secretive conversations are interrupted?
Here a research group from CheckPoint who’ve successfully manipulated the messenger’s protocols and parameters to crash the app of those group participants.
Breaking In
The team has crafted a specific tool as WhatsApp Manipulation Tool, that’s capable of performing the below operation.
In a general course, when a participant in the group sends a message to the group, the app would check the participate’s parameter (as his phone number) to identify who has sent the message and then to broadcast it into the group. With the manipulation tool as said above, the team is able of access those parameters and edit them as they need.
To perform the crash, the attacker needs to modify this parameter of the sender to a “null” value. This is possible when the parser of the participant’s phone number mishandles the input, as the tool allows to do so. Here, they’d trick the parameter as a phone number to a non-digit string, eventually resulting in a null value.
While the manipulation tool is capable of breaking into the protocol and gaining the encryption and decryption keys (used for parameter modifying) and the actual parameter, attackers can affect those group participants to crash their apps. This was first discovered in August this year and was reported to WhatsApp, where the company has fixed it in the version of 2.19.246.
The Crash Loop And Recovery
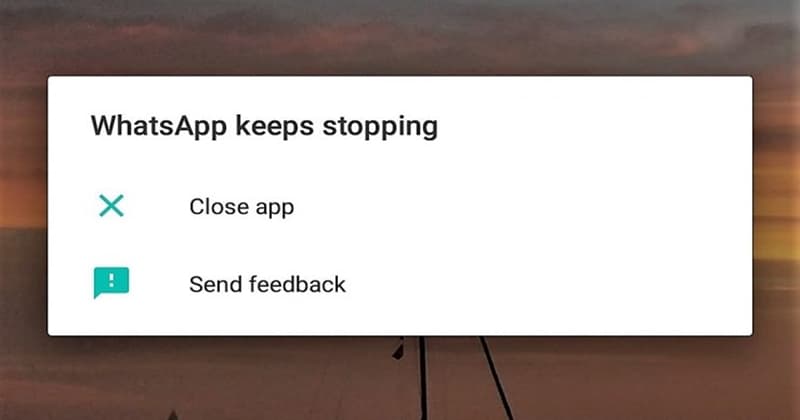
If the above technique is successfully deployed, then a message sent from the participate would crash everyone’s app in their devices. The bug keeps on crashing the app even after tried reopening, locking the user in the crash loop! Further, this action bars the user from accessing the group and needs to be deleted for stopping the crash, which, painfully, deletes the data within. Any important files, images or texts would be gone.
In order to regain control onto this messenger, one has to uninstall and reinstall the app and should be deleting the group that has malicious code of this crashing.


