Every well-established business needs to maintain a robust security system to check for its existing vulnerabilities. In addition, since most of the businesses are now online, you need to look for every loophole for better security. And that’s where the vulnerability tools play a significant role. They help you make your business or organization more secure and foolproof from intruders.
A vulnerability Scanner discovers all exposed endpoints of your network system. Being alert about your vulnerabilities allows you to prioritize your weak areas. You can then access the full safety of your remote workforce and prevent anonymous attacks.
However, choosing the right tools for your level of requirements requires a lot more than you think. Hence, to ease your task, we have mentioned a few alternative options you might like to consider.
Also Read- Best Open Source Intelligence (OSINT) Tools
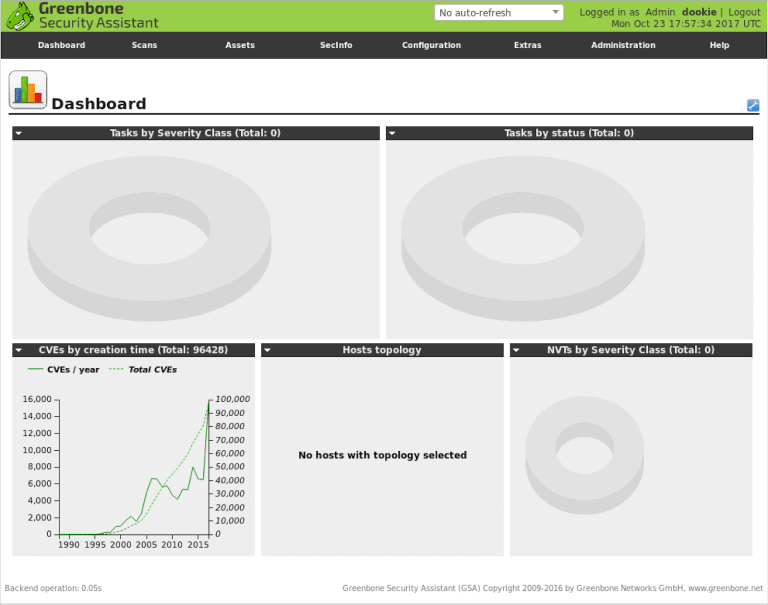
1. OpenVAS Vulnerability Scanner
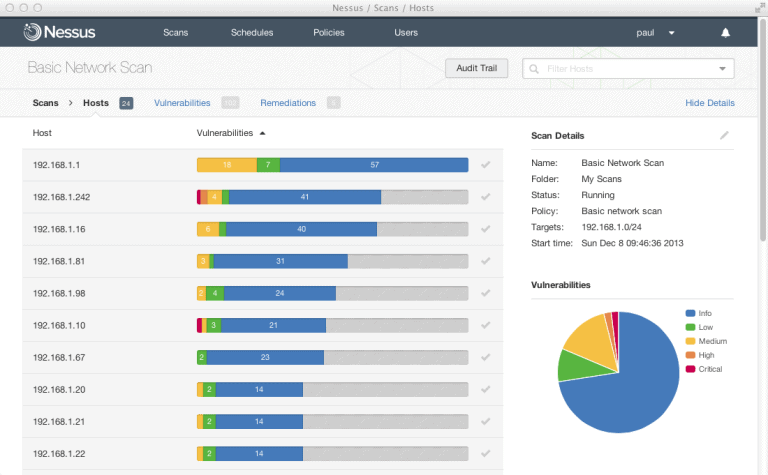
2. Nessus Vulnerability Scanner
3. Comodo HackerProof
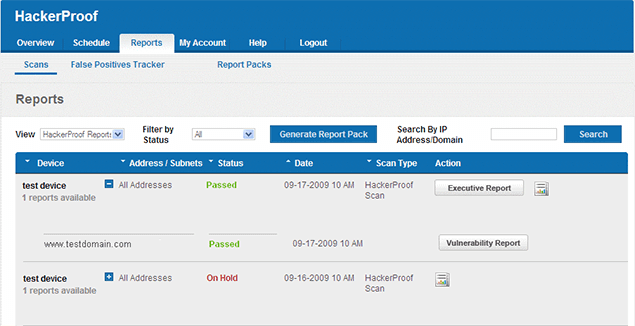
This actually helps in large business modules to generate more revenue, build trust with customers, enhance conversions, and so on.
4. Paessler PRTG
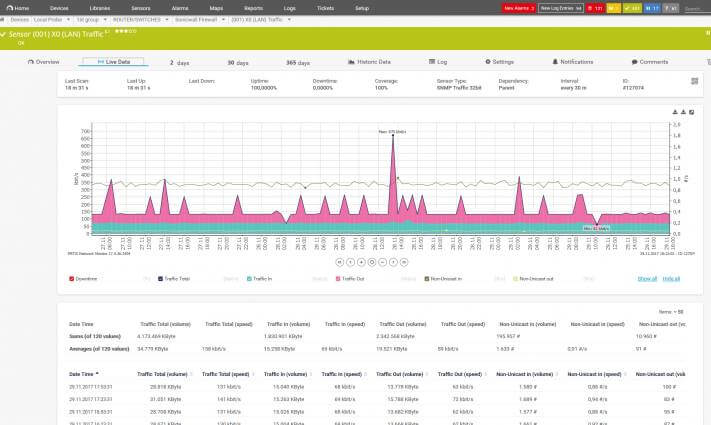
Moreover, it monitors any functional changes in the status and alerts you immediately the moment it detects one. Finally, since you can use the complete tool in its trial version, it gives you a better idea before purchasing the premium version.
5. Tripwire IP360
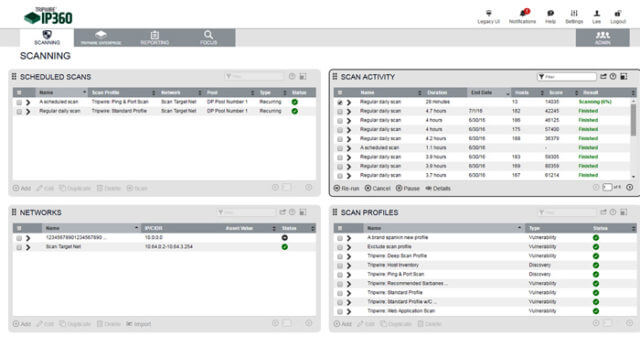
Apart from that, it offers full network visibility by accurately identifying all assets on your network. Above all, it just won’t bother you with unwanted alerts. Rather, it focuses on whatever matters the most.
6. Rapid7 Nexpose

7. Netsparker
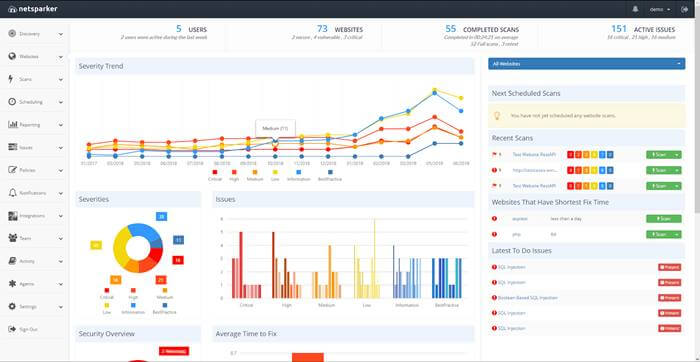
Netsparker is well-known for its accuracy. Thus, you can try the demo version to ensure efficiency before making a direct purchase.
8. Vulnerability Manager Plus
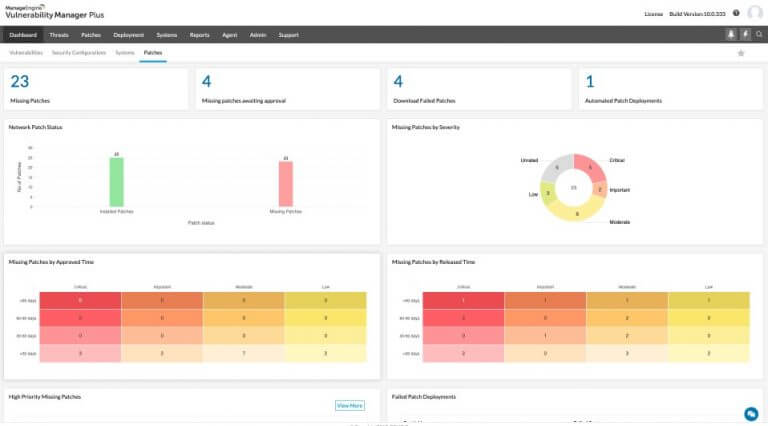
It scans for vulnerabilities, security misconfigurations, high-risk software, and web server misconfigurations. Since it allows you to look from a hacker’s perspective, you can identify every minor flaw for each end-point.
From Editor’s Desk
Finally, as we have reviewed the top tools for vulnerability scanning, we hope you have found a better option by now. These tools offer effortless tracking of minor endpoints and help overcome them. Furthermore, it is now much easier to escape from further hacker attacks.



