While the PC community is fighting for the best processor among Intel and AMD, new research reveals the AMD CPUs have a vulnerability that can expose sensitive data to be leaked from ongoing processes. A bunch of researchers from two universities found that AMD CPUs that came in between 2011 to 2019, is possessed with loopholes pertaining to the L1D cache way predictor, a feature within them.
Flaws in the cache system?
The research team claims to be notifying AMD about three vulnerabilities back in August 2019, but the maker didn’t address them yet. The new potential attacks will be targeting a feature called L1D cache way predictor, a CPU performance related function that deals with how the cached data is processed within memory.
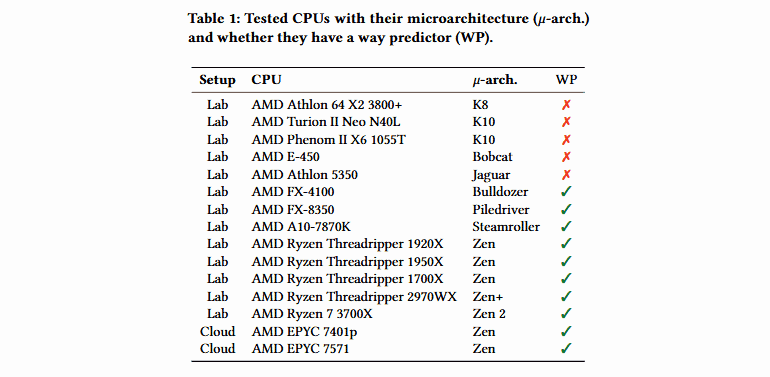
This was present in all those AMD chips, which has Bulldozer microarchitecture and produced from 2011. This flaw was surfaced by researchers at the Graz University of Technology in Austria and the Univerisity of Rennes in France. These six-team people have reverse-engineered an “undocumented hashing function” within AMD that would handle μTag entries L1D cache way predictor.
The two potential attacks
The team has gathered enough information about the functions inside to outlay the exact mechanism that’s happening inside the L1D cache way predictor. This led them to find two new vulnerabilities as Collide+Probe attack and Load+Reload.
Similar attacks as such were practiced on Intel chips in past, calling them Flush+Reload and Prime+Probe. Here, these two attacks can be performed to know how the processes work within AMDs cache and leak them. Though these were hard to capture, experts believe the threat could be highly dangerous if not patched soon.
Unlike Intel’s vulnerabilities, these newly found AMD flaws can be exploited easily without any physical presence, connecting to ports of CPU or any special device, but rather, simple software. Researchers here have trail exploited these flaws with JavaScript in a Cloud Computing environment and exfiltrated data at a speed of 588.9 kb/s. This shows how potential the threat could be if fallen into wrong hands. Yet, AMD hasn’t released any firmware update for this.
Via: ZDNet



