To help customers tackle the attacks on their online API servers, Cloudflare has launched a protective feature called Cloudflare API Shield. This would be available to all Cloudflare customers irrespective of their pricing tiers and should be embedded by admins to make it work. This works by blocking all data requests from devices failing to authenticate.
Cloudflare Launched an API Protection
Application Programming Interface (API) is simply an interface of an app, that would let others eligible apps to procure data through requests. More specifically, it would act on predefined actions like redirecting the data requests to a designated library.
It can be embedded in apps in several ways, like in a standalone app to let internal components communicate with each other, or web-based systems that remain online and process requests from clients like external servers, mobile phones, users, etc. And since these are web-based, they are prone to attacks like command injections, automated login attempts, user data enumeration, etc.
Latest industry reports reveal that attacks on these web-based APIs have increased exponentially since more companies are now moving to cloud-based infrastructure. Web-based APIs are so integral in cloud-based infrastructures since they hold all of the companies devices and severs. While these are reported to be increasing, Cloudflare has come to rescue.
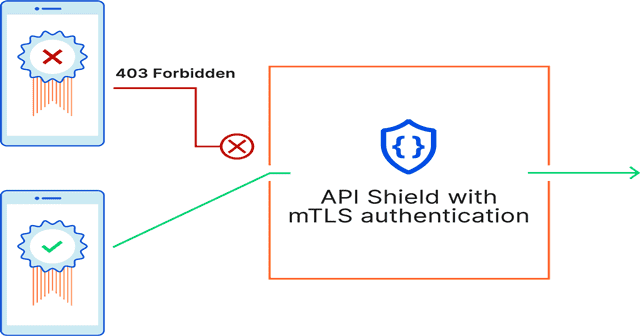
The company has launched a tool called Cloudflare API Shield, that protects users from potential attacks. It’s available for all the Cloudflare customers and requires admins to set up initially. Creating this would produce certain cryptographic keys and certificates which have to be installed on client devices like web servers, IoT devices, mobile apps, etc.
Thus, the API Shield blocks all requests from devices that fail to produce the said cryptographic keys and certificates, thereby thwarting any malicious attack. Based on customers’ responses, Cloudflare said it would be increasing the security features and support for more schemes like gRPC binary protocols later.



