DoppelPaymer is the new group joining Maze ransomware’s pursuit. It has now set up a website named Dopple Leaks to publish their stolen data of those who didn’t pay the ransom. While this is to shame those victims, we see a gradual movement of ransomware groups onto publishing data rather than leaving victims if not paid. This act enables them to get more payments as proved by Maze ransomware.
DoppelPaymer is an offshoot of BitPaymer, another infamous ransomware group that steals data before encryption of files. This method of stealing data before encryption has far been successful to several ransomware groups, as they could further warn victims with excerpts of data to make them pay. And if they don’t surrender, their data will be publicised to shame them.
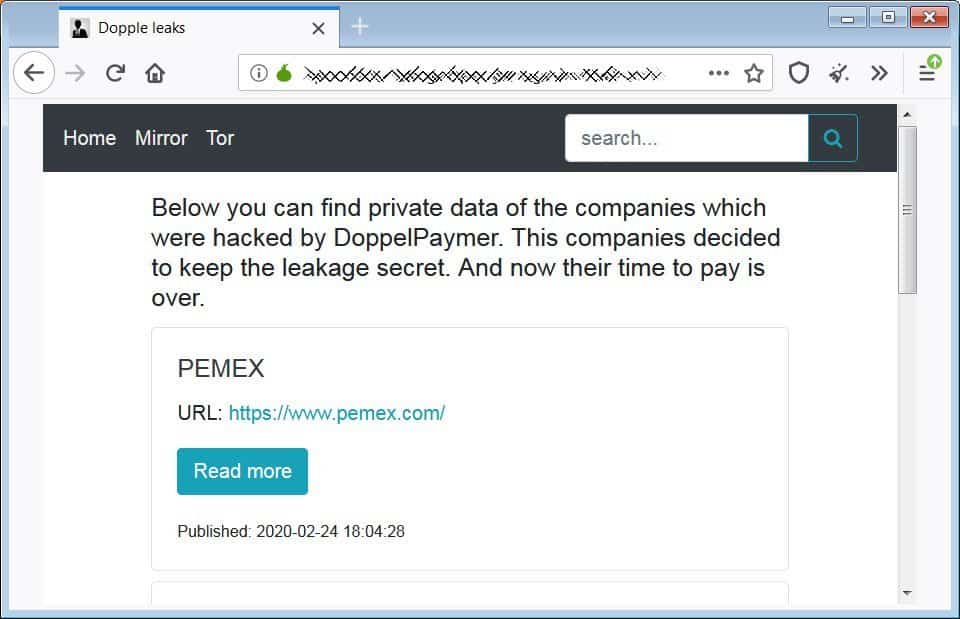
The Shaming Website

The Dopple Leaks started by DoppelPaymer will have the data of those firms that either refused to pay the ransom or exceeded their deadline. This may make them shame within the public and attract government agencies to find them. This tactic of extortion was first started by Maze group, followed by Sodinokibi, Nemty and now DoppelPaymer.
Their darknet site Dopple Leaks has currently four companies’ datasets, as procured by BleepingComputer. The victims are:
- Mexico’s state-owned oil company – Pemex, which was attacked by DoppelPaymer on November 10th, 2019, has been demanded 568 bitcoins ($4.9 million at the time) for a decryptor.
- A merchant account company from the USA, which was asked for a ransom of 15 bitcoins ($150K).
- A logistics & supply chain company from South Africa which was hacked on January 20th, 2020, was asked a ransom about 50 bitcoins ($500K).
- A French telecommunication and cloud services company demanded a ransom of 35 bitcoins ($330K)
Further, the owners of Dopple Leaks said to BleepingComputer that, they’re currently in a test mode and in pursuit of publishing few files of total data, shaming those non-paying customers.
Until and unless data collection firms treat ransomware as data breaches, these publications won’t stop. As BleepingComputer said, companies should be transparent about the data breaches and ransomware attacks to let the public know how they’re affected. And these should be treated sensitively due to confidential information breach.
Via: BleepingComputer



