Two Zero-day vulnerabilities found in DrayTek routers were exploited by two different hackers for months, and have been using it for spying. Hackers in here were seemed to have different motives, as though they got access to numerous devices, they’re just limiting themselves to spy and plant backdoors in the network. And to stop this growing bigger, DrayTek has released patches for binding those Zero-day vulnerabilities.
This was first detected by Qihoo, a Chinese internet security firm that published a report explaining the exploitation. This revealed two different hacker groups exploiting two different Zero-day vulnerabilities available in DrayTek’s enterprise routers, especially routers as Vigor 2960, 300B and 3900. The modus operandi of attackers is as follows:
Group A – Spying the traffic
As there’s no identification yet, the first hacker group was named Group A and has been active since December 4th as per Qihoo reports. It further says the group attacks in a complicated way of abusing the RSA encrypted login mechanism, so as to plant and hide their malicious code in the username login space. And when the DrayTek devices received the encrypted credentials, it’s decrypted and gives hackers access to devices, thus the entire network.
Though having complete control, attackers didn’t intend to spoil after all. As they have planted and running a script in various ports for recording traffic of emails (FTP, IMAP, SMTP, and POP3). And the collected data is packed and sent to the hacker’s remote C2 server every Monday, Wednesday, and Friday. This is typical, as they do not intend to launch any DDoS attacks or fraudulent traffic rerouting, but spying. This may lead to a whole new attack if not stopped.
Group B – Planting backdoors
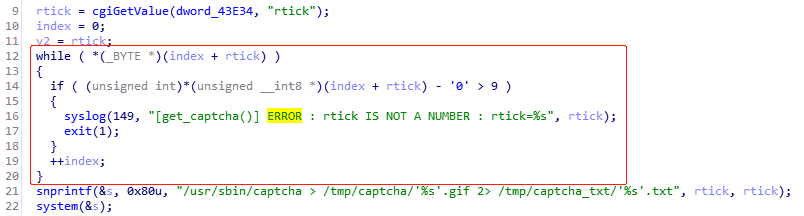
The other attacking group, Group B isn’t that sophisticated as their counterparts, but good at exploiting available vulnerabilities. The group here abused a bug in the trick process, to execute a malicious code and plant backdoors of all vulnerable devices. This was first realized in January and published by Skull Army Blog, which was picked by Group B attackers just two days after to exploit it.
According to ZDNet, a scan by BinayEdge revealed over 978,000 vigor devices that are exposed to potential threats. But it’s good that DrayTek has already released patches. These were released on February 10th right after realizing the attacks by Group B in January and recommends to patch them immediately.
Source: Qihoo’s Netlab



