Sharing your credentials is always a bad thing. Though insisted by firms not to, most of us do for gaining a few little advantages. And here’s one such service which took users’ Instagram login credentials and inadvertently exposed them openly for anyone to see! All this, for the exchange of popularity.
Visible Credentials
Social Captain, a service that claims to increase users Instagram followers by specifically targeting traffic/hashtags/accounts etc. Though it’s having thousands of followers, this platform is turned to be following loose security measures. Anyone interested in trying this service should connect their Instagram account to Social Captain platform, that’s by logging into Social Captain with Instagram login credentials.
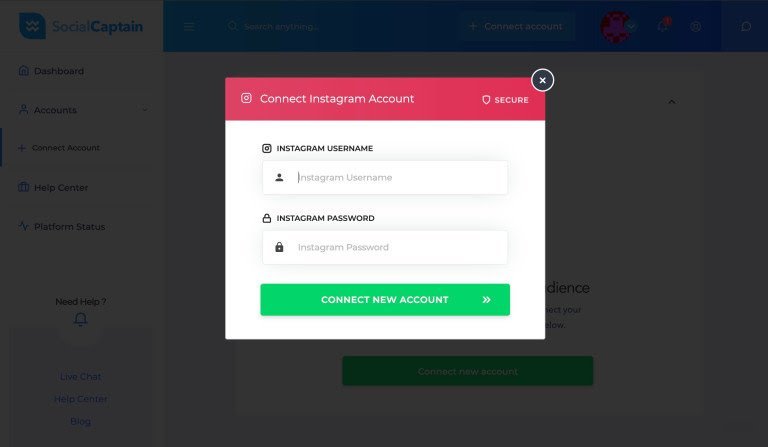
After which, the user can choose to gain traffic by selecting several ways if targeting accounts. TechCrunch, who first reported this incident claims that a researcher has handed them a sample database of 10,000 exposed accounts, that were scraped from Social Captain’s vulnerability. As explained, the platform is storing the sensitive credentials unencrypted, making it visible to those who log in by exploring the site’s source code.
And The Worst
This issue was primarily found to be limited to self-accounts but later turned serious. Not only those who log in to Social Captain can see their credentials in source code in plain text, but if tried, can see other accounts too! This is possible by slightly modifying the URL of Social Captain’s web address with Unique User ID and going through the source code again, thus, revealing the username and password of that specific account.
After being informed by TechCrunch, Social Captain has immediately secured this vulnerability. While the Instagram responded saying that it would take appropriate action on this, Social Captain’s CEO, Anthony Rogers said,
“As soon as we finalize the internal investigation we will be alerting users that could have been affected in the event of a breach and prompt them to update the associated username and password combinations.”



