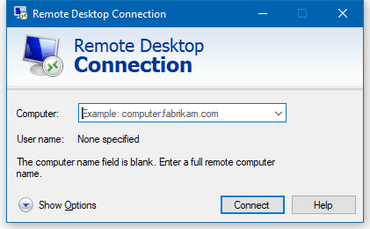
Microsoft has terminated RDCMan, a long served tool from its app list today. Remote-Desktop-ConnectionMan lets any desktop user control other desktops in a network via RDP. This tool rose to popularity in the late 2000s, but Microsoft introduced other default RDP tools to communicate better. And now, after finding an internal bug, the maker decided to discontinue it altogether.
A well-known feature
Completely disabling a popular service is always seen as an extreme step. Just like Avast did with its JavaScript earlier this week, now Microsoft did with RDCMan. The tool was previously used among Microsoft internal employees for communication but later released as a tool to be downloaded for users. Ever since it was let out, users installed it as a third-party app and relied on it for quick remote controls.
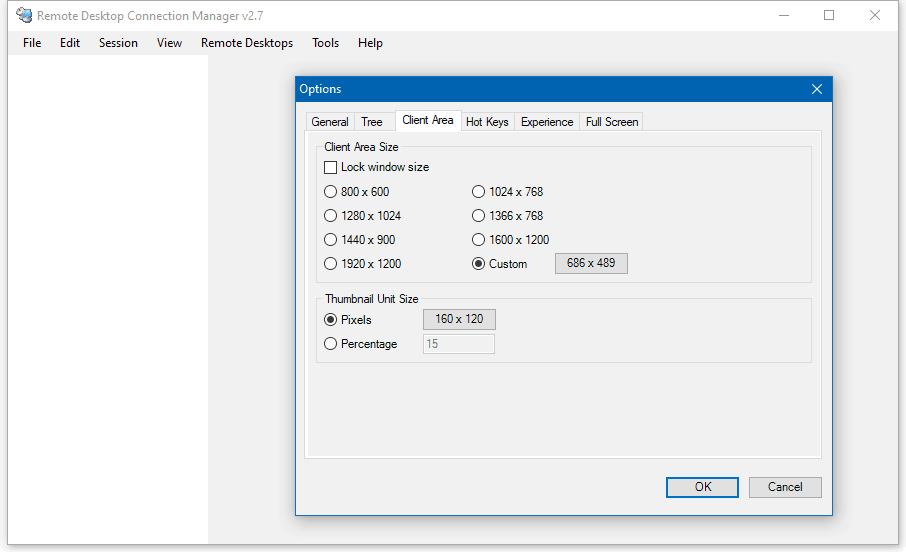
RDCMan gained traction due to being a free RDP tool in the early 2010s, but Microsoft wanted users to shift away from it eventually. So it introduced other RDP alternatives as Official Remote Desktop app and a Remote Management tool (MSTSC). It even stopped updating the RDCMan since 2014, where it passed the last update as v2.7. Yet, there are few people using this app to date.
The Bug
Microsoft’s intention of removing this feature completely strengthened even more after finding an internal bug. RDCMan is said to possess a bug that may allow a remote attacker to retrieve data from any RDCMan installed PC. For this “an attacker could create an RDG file containing specially crafted XML content and convince an authenticated user to open the file” said Microsoft.
This added reason led Microsoft to take an extreme, yet anticipated step in disabling the feature completely. It further advises users not to open any unsolicited RDG files from unknown sources. And strongly recommends users to migrate from RDCMan to other alternatives.



