Microsoft disclosed a new range of attacks happening against Kubeflow servers and being used for cryptocurrency mining. Since high-power machines are desirable for cryptocurrency mining, attackers here are targeting Kubeflow servers, which run Machine Learning operations, thus have adequate computational power. Attacker here is looking for admin panels that are open to the internet and hijack them.

Cryptomining is a new form of robbery. Implanting the malicious miner somehow will lead to persistent income until the victim detects and vanishes it. Adversaries often look for higher powered systems that have GPUs, as these do more minting and garner much. And what could be a better machine that’s dedicated to Machine Learning? Networks like Kubernetes clusters are desirable as they have more computational power.
Targeting ML Kubernetes For Cryptomining
As Microsoft reported today, they’ve found tens of Kubernetes clusters running Kubeflow being targeted for Cryptomining. Kubeflow is a toolkit for running Machine Learning programs over Kubernetes clusters. Attackers here are searching for Kubeflow admin panels that are misconfigured and open on the internet.
Most of the Kubeflow admins who changed their default settings, and exposed the admin panel on the internet are vulnerable. By default, these admin panels are accessible only within Kubernetes clusters. Ans since the attackers are scanning for exposed misconfigured machines, they deploy new sever images focused on XMRig software, a cryptocurrency miner.
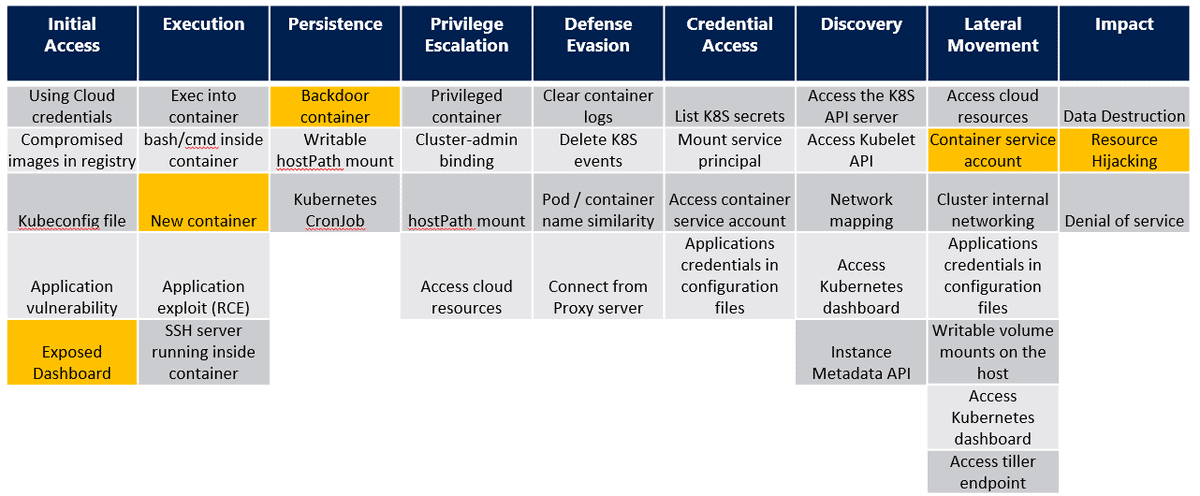
This miner uses the extensive resources of the victim’s machines and mint coins for the attacker. Microsoft has been tracking these attacks since April this year and found that attackers have moved from general Kubernetes to Machine Learning Kubernetes clusters. And to evade, Yossi Weizman, a security researcher at Microsoft’s Azure Security Center, suggested below steps to check:
Firstly, verify whether the malicious container is deployed or not in the cluster. Check this by typing following command;
kubectl get pods –all-namespaces -o jsonpath=”{.items[*].spec.containers[*].image}” | grep -i ddsfdfsaadfs
And of the Kubeflow is found in the cluster, secure the dashboard immediately. Exposing it to the internet is the main source of being attacked. Check this by typing the following command and make sure that it is not a load balancer with a public IP:
kubectl get service istio-ingressgateway -n istio-system
Via: ZDNet



