China Noted 33 Apps That are Collecting Unnecessary User Data
After receiving complaints from several users, the Cyberspace Administration of China (CAC) has listed 33 apps that were said to be collecting unnecessary personal...
US DoJ: SolarWinds Hackers Accessed Email Accounts of 27 Attorney’s Offices Employees
The US DoJ revealed that Office 365 email accounts of employees at 27 US Attorney's offices were beached in the SolarWinds attack last year.
Hitting...
IKEA is Under an Email Reply-Chain Attack, Warns Employees
IKEA is suffering from a reply-chain attack, where its employees are being targeted with malicious links spread through internal emails.
The furniture is thus asking...
CISA Listed 17 New Actively Exploited Vulnerabilities, Advises to Patch
The US Cybersecurity and Infrastructure Security Agency (CISA) has added 17 new vulnerabilities to its list of "Known Exploited Vulnerabilities Catalog."
These vulnerabilities are actively...
Fake WhatsApp Support Teams Aimed at Stealing Sensitive Data in Wild
WaBetaInfo reported on a malicious campaign where unknown fraudsters are pretending as WhatsApp Support personnel to steal sensitive information from people.
As per it, they're...
Apple Patched Two Critical Bugs in iPhone, iPad and Mac
Apple today released an important security update to three of its devices - iPad, iPhone, and Mac to patch two critical zero-day vulnerabilities in...
RapperBot is Capturing IoT Devices to DoS Attacks on Game Servers
Fortinet researchers have detailed a new campaign of the RapperBot gang, which is now targeting IoT devices for conducting DoS attacks against game servers.
In...
PII of 45,000 Students From New York City Education Department Leaked
The New York City Department of Education is the latest victim in the MOVEit Transfer attack, where it reported that sensitive data of around...
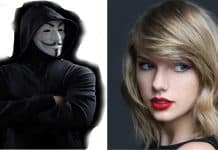
MyKings Botnet Is Hiding Its Malware Behind Taylor Swift’s Image
A popular botnet group is currently using the image of Taylor Swift to shield themselves from virus scanners. The objective of this methodology is...
Google Authenticator App Has 2FA Code Stealing Flaw
Security researchers found that even Google Authenticator app isn't reliable for secure logins. ThreatFabric researchers found malware that's capable of stealing 2FA codes from...