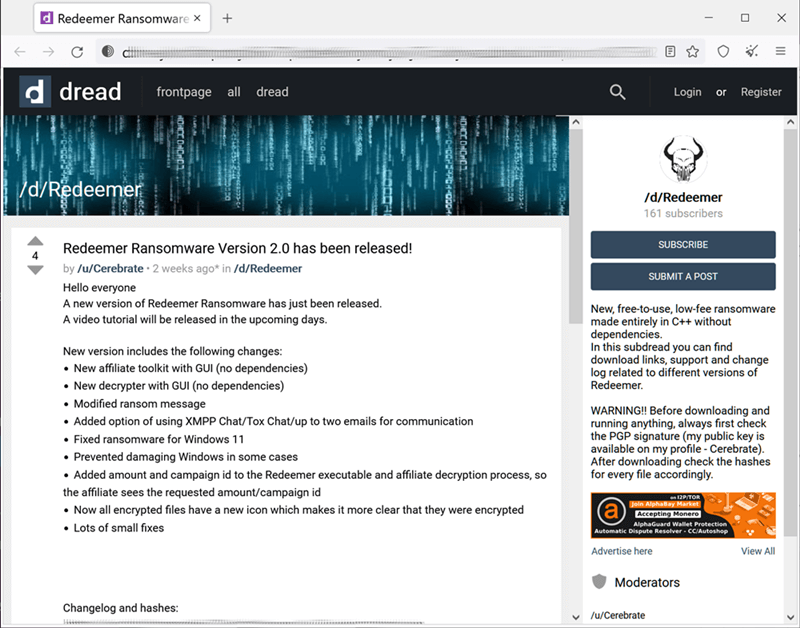
The author of Redeemer ransomware is promoting his malware’s 2.0 version in hacker forums, hoping to get affiliates and earn a part of their ransom payments.
This new version of Redeemer is sold for free, with instructions on how to use it enclosed in the zip file. Security researchers who tested the Redeemer 2.0 said the malware is updated to include Windows 11 systems, having a GUI, and other new features.
Redeemer 2.0 is Out For Free
Researchers spotted that the author of Redeemer ransomware is advertising an updated version of his malware for free in the underground hacker forums. Though he’s letting anyone take it, the author takes a 20% commission in case of successful ransom collection by the affiliates.
The author mentioned that Redeemer 2.0 is written entirely in C++, supports multi-threaded performance, a medium AV detection rate, and adds Windows 11 to its arsenal of exploitable machines alongside Windows Vista, 7, 8, and 10.
Researchers at Cyble tested this new ransomware and said the malware is capable of exploiting Windows APIs to execute itself with admin privileges. And before encrypting, it clears the event logs and deletes shadow copies and any system backups to prevent easy restoration by victims later.
Also Read- Google Chrome is Testing a Native Note-Taking Feature
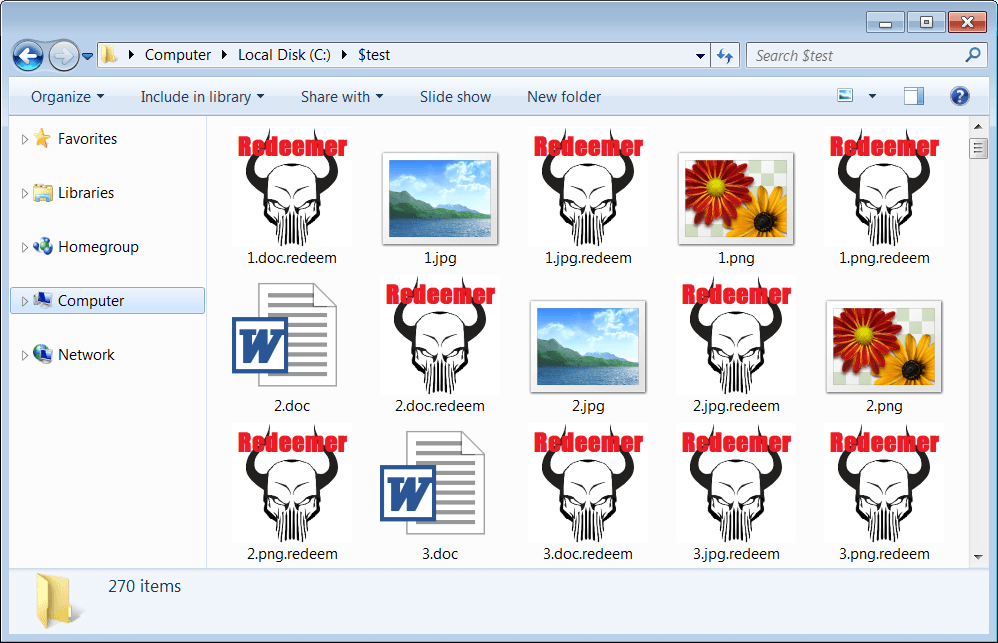
Also, it kills a number of legitimate processes to make a smooth encrypting operation, drops a custom icon, and appends its name to the extension of the encrypted files. It also embeds the ransom note in the Winlogon registry key, so the victim can learn more and proceed to pay ransom.
Redeemer 2.0 author mentioned that he’d share the master key to be combined with the private build key held by the affiliate for decryption whenever there’s a successful ransom payment happening.
He also mentioned that the project will go open-source, in case they lose interest. The same happened with Redeemer 1.0 last year. Researchers note that this could be a problem for the community, as leaving the ransomware’s source code open will give rise to new malware varients for more exploitation.