Sodinokibi ransomware is turning critical every day. The group has already exposed a firm’s data last week and even encrypted a temple’s network just recently. Now, the attacking group hacked an automotive firm and threatening it to pay the ransom in time. If not, the data will be sold on online data exchange forums after the due date.
Warn and Publish
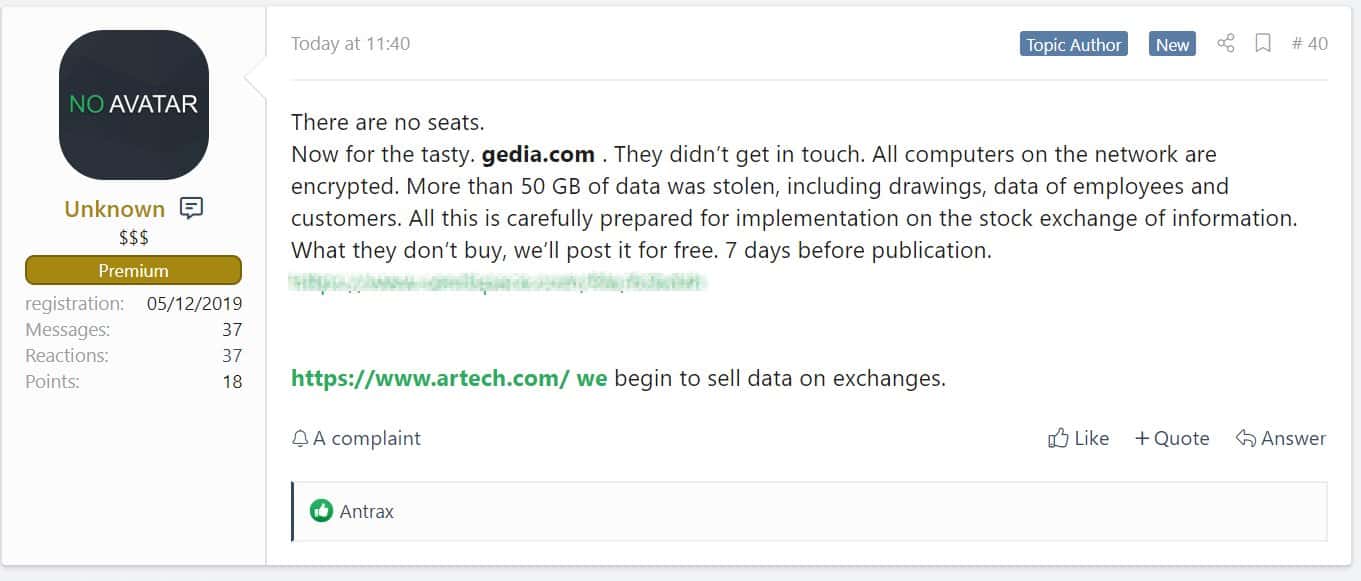
The group’s now threatening an automotive firm, GEDIA Automotive Group to publish their stolen data soon as they have failed to get in touch and pay the ransom. GEDIA is a German automotive firm that supplies auto parts to other makers. With more than 4,000 employees, it has production houses in many nations.
The ransomware group has published an Excel spreadsheet, that contained information and AdRecon report in an Active Directory Environment. This was similar to their previous operations as with Archtech case too. The stolen data is said to be 50GB containing drawings, data of employees and customers which will be published onto data stock exchange soon.
They said, “Now for the tasty.gedia.com They didn’t get in touch. All computers on the network are encrypted. All this is carefully prepared for implementation on the stock exchange of information. What they don’t buy, we’ll post it for free 7 days before publication”
The New Game
Ransomware groups are changing their plans to a much effective way recently. They’re not just encrypting the systems, but also stealing the data before doing so. This let them threaten the victim to surely pay the ransom. And if not complied, the attacker would leak the stolen sensitive data in parts until they pay it.
While publishing the data is one way of exploiting them, selling it to other malware groups for future targeted attacks could be highly effective. This data may be useful for sending phishing emails with spam links to infect users with malware and steal the data further.
Source – BleepingComputer