VPNMentor has released a report saying how a database of 300 million records is being used for credential stuffing Spotify accounts worldwide.
While this database’s origin was unknown yet, hackers have been using it for accessing Spotify accounts and selling them to others. It was reported to Spotify in July, and it did a rolling reset to all affected accounts.
Credential Stuffing Attack on Spotify
Spotify is the largest music platform by userbase, which is having users from around the world. It’s so popular that potential users are interested in paying for a lesser price if a subscription is available.
Thus, catching that demand, hackers have been breaching the Spotify accounts and reselling them to interested customers for profit.
One such incident has been happening this year, and VPNMentor’s report throws light on how that’s happening.
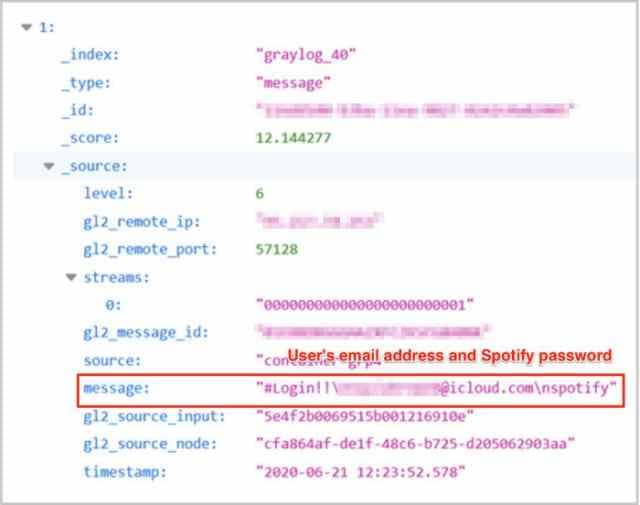
The researchers mentioned that a database containing over 300 million users’ records (has username passwords, e-mail addresses, etc.) was being used by hackers to credential stuff on Spotify accounts.
Credential Stuffing is a technique where attackers use a list of usernames and passwords to try them matching on other online accounts of a targeted user.
This is based on the hope that the victim should be using common login credentials for his other online accounts. Thus, they can breach and takeover such matching accounts.
The list for trying out here could be obtained from previous hacks and data breaches. And this could be the same case in Spotify’s too. VPNMentor said that a database of 300 million records was being used for compromising 300,000 to 350,000 Spotify accounts.
This was reported to Spotify in July this year and received a reply on the same day as “In response to our inquiry, Spotify initiated a ‘rolling reset’ of passwords for all users affected. As a result, the information on the database would be voided and become useless.” Yet, Spotify users are recommended to reset/change their passwords for strong and unused ones for better security.