Apple was just granted a patent that lets the company make iPhones sharable among several users. This adds individual user accounts to the devices and is accessible by users with their respective passcode authentication. Apple stressed much on doing this securely and also talked about passcode throttling.
A Multi-User Access to Single iPhone
Apple doesn’t think so, as it has just received a green signal to one of its patents that will let the iPhone maker create secure rooms in an Apple device. As mentioned in the patent, it’s intended to bring this feature to laptops, Macs, and iOS devices like iPhones and iPads.
Related Post- Apple Autonomous Car May Start Manufacturing in 2024
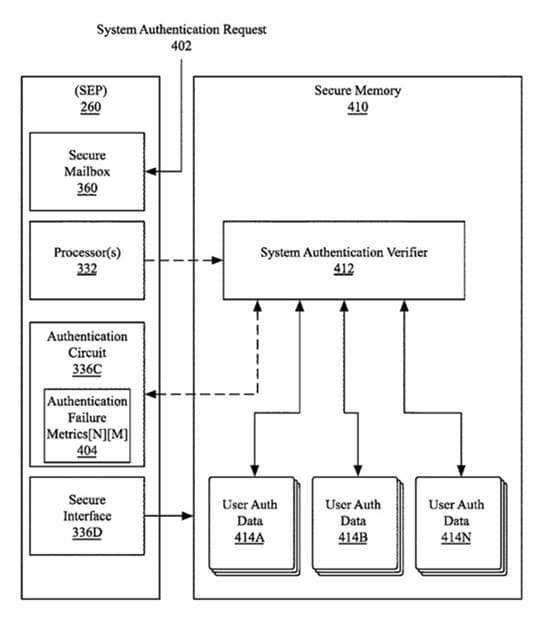
Thus, a user will be asked to enter his respective passcode to access his own data on the device. This may divide all the system data based on users, from app passcodes to Apple Pay. At the same time, some services like the browsers should be shared.
Also, Apple talked about malicious attempts could be made by threat actors to gain access to the device and extract data from memory. Thus, it’s focusing much on securing this type of access, more than the functionality it provides. It’s detailed about effectively using the Secure Enclave Processor in this.
The company has also mentioned passcode throttling, where it will deliberately slow down the device after failed login attempts. This will let users be cautious about entering their passcodes correctly, and at the same time, will frustrate the attacker’s brute-force attempts.
Also Read- Zero-Click Vulnerability in Apple iMessage Exploited to Spy on Journalists



