Researchers at Malwarebytes have discovered a campaign of unknown hackers, who’re actively exploiting the Windows Error Reporting service for malicious file injection. They exploit this legitimate Windows tool to remain stealthy, and also to execute their malware in the system’s memory, thereby leaving no footprints of attack.
Hackers Exploit Windows Tool in File-less Attack
Researchers Jérôme Segura and Hossein Jazi from Malwarebytes have surfaced a new hacking campaign, where the perpetrators are exploiting a legitimate Windows tool called the Windows Error Reporting (WER) service. More than letting the user know about an error, it’s used by Microsoft to stay informed about user issues in Windows.
The hacking group tracked by researchers, who’re yet to be named, are active since September 17, where the first attack was recorded. They say the mode of reaching the target is through a spear-phishing, where a malicious document was embedded in the email, touting as a Workers Compensation document as the lure to be opened.
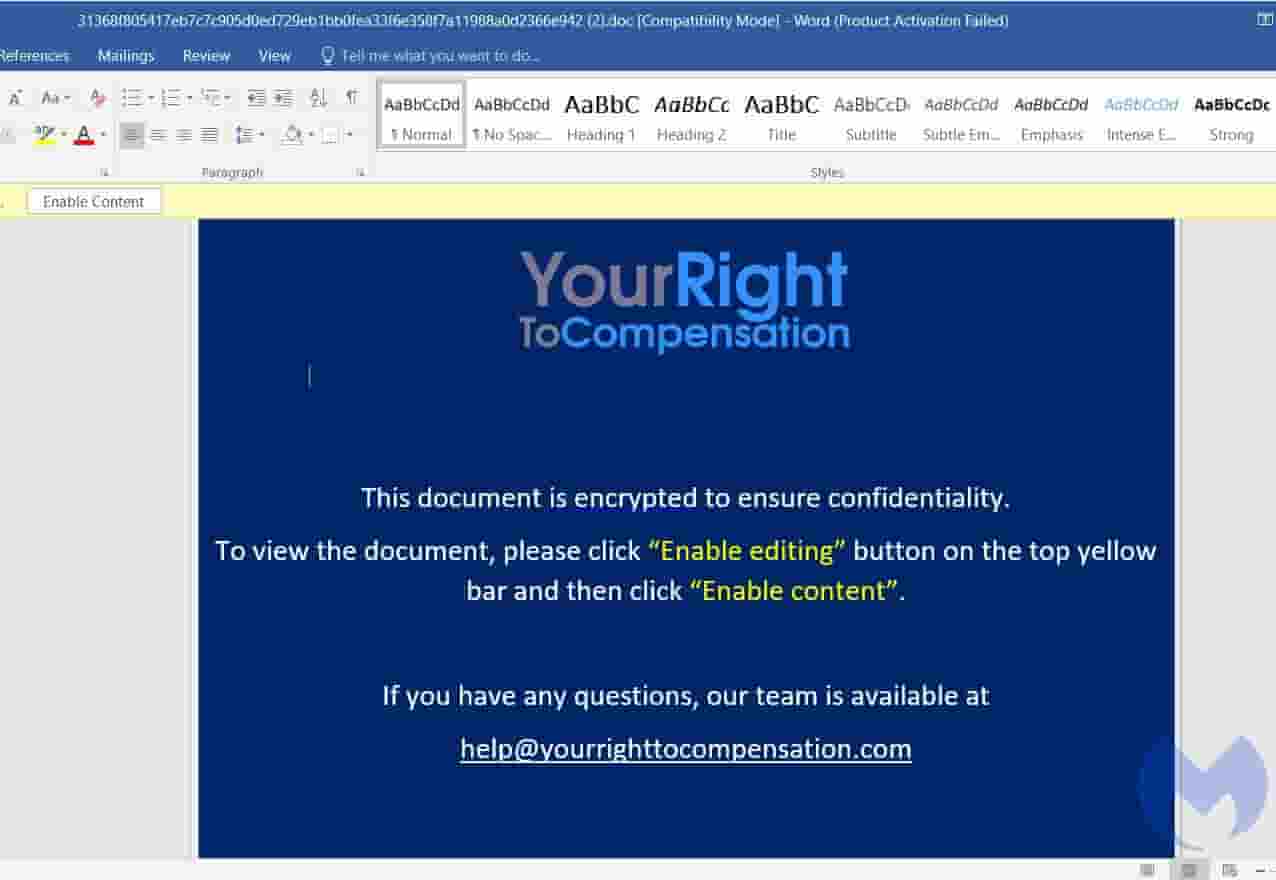
Upon opening, it will then prompt the users to enable macros and editing of the content, which in the background starts running a shellcode through a CactusTorch VBA module. This will “load a .NET payload straight into the now infected Windows device’s memory” says BleepingComputer.
Next, this will be executed in the system’s memory, which leaves no traces on the hard drive. Also, it injects an “embedded shellcode into the WerFault.exe, the WER service’s Windows process.” The newly created Windows Error Reporting service thread that’s infected with the malicious code will check for safety go through.
It checks for any debugging or signs of running in a sandbox or virtual machines, and if deemed safe, it will then proceed to the next step of loading the final shellcode “in a newly created WER thread, which will get executed in a new thread.” It’s found that the final payload was being imported in the form of fake favicon.
Researchers were unable to study it ultimately, since the final payload, loaded from a site termed as “asia-kotoba[.]net” was down while analysing the attack. Yet, from a few clues gathered in the process, they linked the perpetrators to be a Vietnamese state-backed hacking group.
Tracked as APT32, the hacking group is also called as SeaLotus or OceanLotus. Usage of CactusTorch VBA module to dump payloads and the domain they’re using (yourrighttocompensation[.]com) for these attacks was registered in the Ho Chi Minh City of Vietnam, hinting it to be the Vietnamese hackers.


